Apparently Linkedin now have a feature that allows users to provide their corporate passwords to a third party so the users can then send invites to other people in their office. I really don’t see how this can Be A Good Thing 😉 – Paul Cunningham has a post on ExchangeServerPro on this feature and links to Adam Fowler’s post on how to block LinkedIn to Exchange. This is interesting as we’ve also seen this issue with Verizon doing something that we expect is screenscraping to provide email information to phones. Admittedly this was a while back but we have found it hitting the Exchange server so it will be interesting to see if this successfully blocks the server.
In a meantime, maybe it’s time to not only educate LinkedIn that this is a really bad idea but also your corporate users.
For what it’s worth the solution is to do the following:-
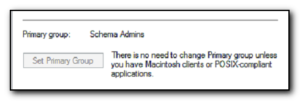
There are a few settings to check. First, under the Set-OrganizationConfig area, you’ll need to check that EwsApplicationAccessPolicy is set to ‘EnforceBlockList’. If it’s not, it’s going to be “EnforceAllowList” and you’re probably OK, as it’s using a whitelist for access to only what’s listed rather than a blacklist, to only block what’s listed.
Next, you need to add LinkedIn into the BlockList. This is done with the command “Set-OrganizationConfig -EwsBlockList LinkedInEWS“